In today’s digital ecosystem, APIs (Application Programming Interfaces) are the backbone of modern applications. They enable systems to communicate, exchange data, and deliver seamless user experiences. However, as APIs become more integral to business operations, they also become prime targets for security threats.
Many organizations believe their APIs are secure because they have implemented basic measures such as HTTPS, API keys, or occasional code reviews. While these steps are important, they often create a false sense of security. Checking a few boxes does not equate to building a truly secure API.
The reality is that API security is not a one-time task—it is an ongoing strategy that requires a deeper understanding of risks, context, and proper implementation of multiple layers of protection.
The Illusion of Basic Security
A common pattern seen in production APIs is the reliance on minimal safeguards. For example:
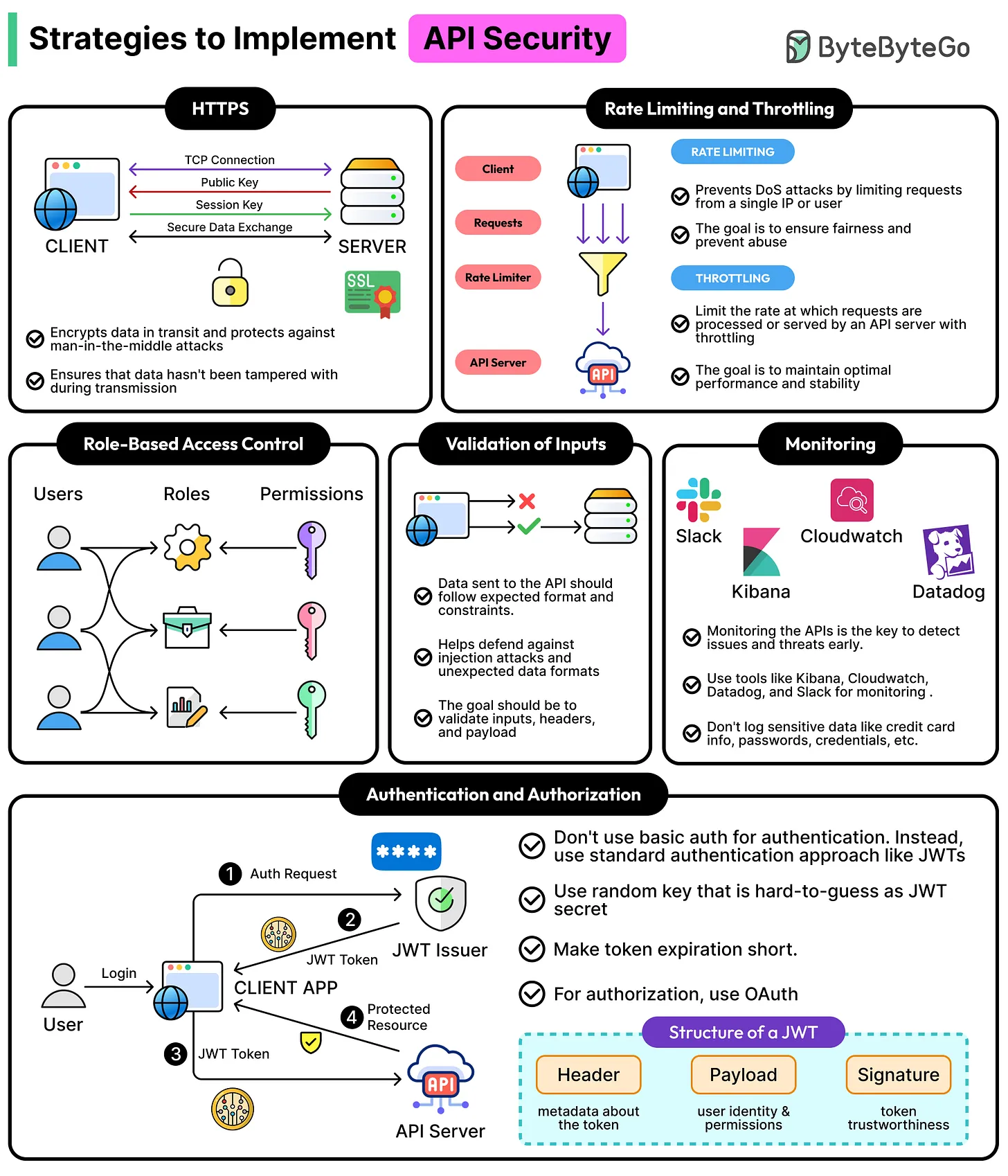
- HTTPS is enabled to encrypt data in transit
- API keys are used to identify clients
- Basic authentication mechanisms are in place
- A quick review is conducted before deployment
While these measures are necessary, they are far from sufficient.
One of the most critical and frequently overlooked issues is the difference between authentication and authorization.
An API may successfully verify that a user is who they claim to be (authentication), but fail to verify whether that user has permission to access a specific resource (authorization). This creates a serious vulnerability. An authenticated user could potentially access data or perform actions beyond their intended scope.
Such flaws often go unnoticed during standard testing because everything appears to work correctly under normal conditions. It is only when someone actively probes the system that these weaknesses are exposed.
Understanding the Core Layers of API Security
To build a secure API, it is essential to think in layers rather than isolated features. Each layer addresses a different aspect of security.
1. Authentication: Verifying IdentityAuthentication ensures that the entity making a request is legitimate. Common methods include:
- API keys
- OAuth tokens
- JSON Web Tokens (JWT)
- Session-based authentication
However, relying solely on API keys is risky. API keys can be easily exposed, shared, or misused. More robust methods like token-based authentication with expiration and refresh mechanisms provide better control.
2. Authorization: Controlling AccessAuthorization determines what an authenticated user is allowed to do.
This is where many APIs fail.
Proper authorization requires:
- Role-based access control (RBAC)
- Attribute-based access control (ABAC)
- Resource-level permission checks
Every request should be evaluated not just for identity, but for intent and scope. For example, a user may be allowed to view their own data, but not someone else’s.
Skipping this step can lead to data leaks, privilege escalation, and compliance violations.
3. Input Validation: Preventing Malicious DataAPIs must never trust incoming data.
All inputs should be:
- Validated for type, format, and size
- Sanitized to prevent injection attacks
- Strictly parsed to avoid unexpected behavior
Common threats include SQL injection, command injection, and malformed payloads that can crash or exploit the system.
A strong validation layer ensures that only expected and safe data is processed.
4. Rate Limiting and ThrottlingAPIs are vulnerable to abuse through excessive requests.
Implementing rate limiting helps:
- Prevent denial-of-service (DoS) attacks
- Control resource usage
- Ensure fair access for all users
Throttling mechanisms can also dynamically adjust limits based on usage patterns, adding an extra layer of protection.
5. Secure Data Transmission and StorageWhile HTTPS encrypts data in transit, security must also extend to how data is stored and handled internally.
Best practices include:
- Encrypting sensitive data at rest
- Avoiding exposure of sensitive fields in responses
- Using secure headers and configurations
Data should always be treated as sensitive unless proven otherwise.
6. Logging and MonitoringSecurity is not just about prevention—it’s also about detection.
Comprehensive logging helps:
- Track unusual activity
- Identify potential breaches
- Support forensic analysis
Monitoring tools can alert teams to anomalies such as:
- Sudden spikes in traffic
- Repeated failed authentication attempts
- Unauthorized access patterns
Without visibility, even the most secure system can be compromised without notice.
Choosing the Right Strategy for the Right Scenario
One of the biggest challenges in API security is not knowing what tools exist—but knowing when to use them.
Different APIs require different levels of security depending on their context:
Public APIs- Require strict rate limiting
- Should use strong authentication (OAuth)
- Must assume exposure to untrusted environments
- May rely on network-level security
- Still require authentication and authorization
- Often overlooked, but equally vulnerable
- Need controlled access with scoped permissions
- Require monitoring and usage tracking
- Should implement contractual security measures
A one-size-fits-all approach does not work. Security must be tailored to the specific use case, risk level, and data sensitivity.
The Importance of Defense in Depth
No single security measure is enough.
A secure API follows the principle of defense in depth, where multiple layers work together to reduce risk. Even if one layer fails, others remain in place to protect the system.
For example:
- If an API key is compromised, authorization rules can still prevent misuse
- If input validation fails, monitoring systems can detect abnormal behavior
- If authentication is bypassed, rate limiting can still mitigate damage
This layered approach significantly reduces the likelihood of a successful attack.
Moving Beyond the “Happy Path”
Many APIs are tested only under ideal conditions—the “happy path.” However, attackers do not follow these paths.
Security testing should include:
- Edge cases
- Invalid inputs
- Unauthorized access attempts
- Stress and load scenarios
By thinking like an attacker, developers can identify weaknesses before they are exploited.
Conclusion: Security Is a Continuous Process
API security is not a checklist—it is a continuous discipline.
Enabling HTTPS or adding an API key is just the starting point. True security requires a comprehensive approach that includes authentication, authorization, validation, monitoring, and strategic implementation based on context.
The most dangerous vulnerabilities are often the ones that are not immediately visible. They exist quietly, hidden behind systems that appear to function perfectly.
To build truly secure APIs, organizations must move beyond surface-level protections and adopt a mindset of constant evaluation, improvement, and vigilance.
Because in the world of APIs, being “mostly secure” is often not secure at all.